Data erasure
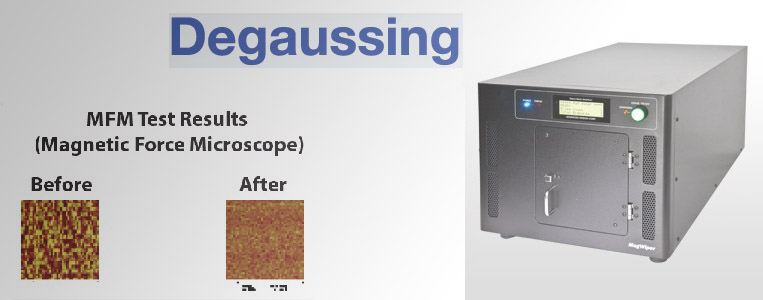
Data erasure (also called data clearing or data wiping) is a software-based method of overwriting data that completely destroys all electronic data residing on a hard disk drive or other digital media. Permanent data erasure goes beyond basic file deletion commands, which only remove direct pointers to data disk sectors and make data recovery possible with common software tools. Unlike degaussing and physical destruction, which render the storage media unusable, data erasure removes all information while leaving the disk operable, preserving IT assets and the environment.
Software-based overwriting uses a software application to write patterns of pseudo-random meaningless data onto all of a hard drive’s sectors. There are key differentiators between data erasure and other overwriting methods, which can leave data intact and raise the risk of data breach or spill, identity theft and failure to achieve regulatory compliance. Many data eradication programs also provide multiple overwrites so that they support recognized government and industry standards. Good software should provide verification of data removal, which is necessary for meeting certain standards.
To protect data on lost or stolen media, some data erasure applications remotely destroy data if the password is incorrectly entered. Data erasure tools can also target specific data on a disk for routine erasure, providing a hacking protection method that is less time-consuming than software encryption. Hardware encryption built into drive firmware and integrated controllers is now a popular solution with no degradation in performance at all.
The firmware can encrypt at 256-bit full AES encryption faster than the drive electronics can write the data. Drives with this capability are known as self-encrypting drives (SED) and are present on most modern laptops and are increasingly used in Enterprise to protect data. Changing the encryption key will make all the drive data inaccessible so is an easy and very fast method of achieving 100% data erasure. Theft of an SED will induce physical asset loss, but data on the drive is inaccessible without the decryption key which is not stored on the drive.
DT Asia provides focused security solutions and services that secure your data at rest, data in motion and data in use. We provide best degaussing service in Singapore, Hard Disk Crusher, NSA degausser Singapore, DoD degausser Singapore, hard disk destruction singapore,erase hard disk singapore, secured hard drive destruction singapore, Hong Kong and Japan.